Update:
Amazon Web Services now offers Free or very low cost SSL certificates for most of their products in many regions around the world, including EC2 instances though their AWS Certificates Manager.
With today’s web, having an SSL certificate on your website that shows a green HTTPS icon in your visitor’s browser is a must. Not only does it drastically help with SEO, it also ensures transactions between your website and your visitor are encrypted and hacker proof-ish to a certain extent. Read on to get all the info on how to setup Amazon Linux SSL using Let’s Encrypt!
How does Let’s Encrypt SSL and Certbot work?
In the past, setting up an HTTPS website with an SSL certificate required recurring yearly fees from a certificate authority like Comodo SSL Certificates otherwise you would trigger the big red “danger danger site” warning on most browsers and scare your visitors to safety.
With the dream of an HTTPS-only web put forward by Google
and other major tech companies, Let’s Encrypt Free Certificate Authority with the help of Certbot automations created the perfect setup to promote a secure browsing experience to web users at a cost every site owner can afford: free.
Simply put, Let’s Encrypt is the Certificate Authority providing the trust certificate and Certbot is the program you will use to install and keep up to date the certificate on your server.
Setting up your Amazon Linux for SSL
Looks easy enough, here’s how to setup your HTTPS Let’s Encrypt certificate on your single website AWS EC2 Amazon Linux AMI instance of predilection. Take note that the process should be very similar for any linux based LAMP server setup.
Installing the mod_ssl module for Apache
First, let’s make sure Apache is running:
1
sudo service httpd status
If not, start it to make sure everything is fine:
1
sudo service httpd start
Now that we know Apache is good to go, we’ll need the mod_ssl module installed and our server up-to-date.
1
2
sudo yum update -y
sudo yum install -y mod24_ssl
Downloading Certbot’s tool
First thing you will want to do is download Cerbot’s tool to setup everything. At time of writing those lines, the URL was https://dl.eff.org/certbot-auto.
Simply login via SSH to your AWS EC2 instance and type this in to download the software:
1
wget https://dl.eff.org/certbot-auto
Then, we will need to make the software executable, changing the rights on the file like so:
1
chmod a+x ./certbot-auto
Generating your Let’s Encrypt Free SSL Certificate
Since, at the time of writing, Amazon Linux wasn’t officially supported, we will need to run Cerbot’s tool in standalone mode with the debug flag on and update the Apache config ourselves.
Make sure that your DNS records are set properly for those domains before continuing!
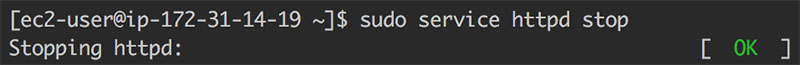
First, let’s turn off Apache so that Certbot can do it’s thing:
1
sudo service httpd stop
Here’s how to do it for the domain “example.com”:
1
./certbot-auto certonly --standalone --debug -d example.com -d www.example.com
Notice the “www.example.com” option added there. You can add as many subdomains as you want using the -d flag. The WWW subdomain is usually needed by most applications, hence why I added it in the example.
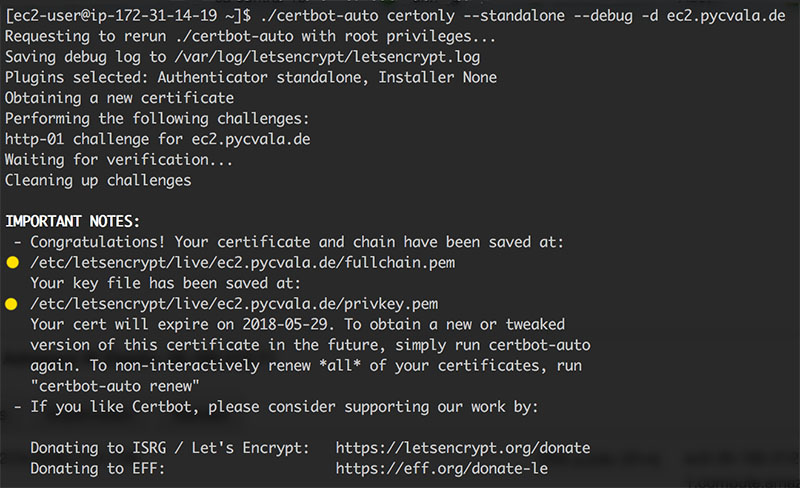
The Certbot will once again do its robot thing and after asking you a few questions hopefully come back to you with paths to your certificate and private key files (as shown in the previous screenshot) for you to add to Apache’s config.
Configuring Apache with your Let’s Encrypt certificate
Now that Certbot has created the required files for you, all you need to do is configure Apache for SSL and where to locate the required files.
While this may vary, Certbot will usually put your certs in the following paths for you:
1
2
3
Certificate: /etc/letsencrypt/live/example.com/cert.pem
Full Chain: /etc/letsencrypt/live/example.com/fullchain.pem
Private Key: /etc/letsencrypt/live/example.com/privkey.pem
Simply edit your Apache SSL config using your favorite text editor, mine being vim.
1
sudo vim /etc/httpd/conf.d/ssl.conf
Now, go find and edit those 3 lines using the provided paths above:
- Set SSLCertificateFile to your Certificate path.
- Set SSLCertificateKeyFile to your Private Key path.
- Set SSLCertificateChainFile to your Full Chain path.
Save and close the file. Now all you need to do is restart Apache and voilà!
1
sudo service httpd restart
Setting up Certbot’s auto-renew job
Let’s Encrypt certificates are valid for 90 days from the time of generation. In order to keep them free-forever, you will need to renew them using Certbot’s auto-renew feature. Just to make sure it’s always valid, I like to run it twice a day, every day with a cron job. If it’s not due for renewal, Certbot will automagically skip the update!
Here’s how to edit your crontab:
1
crontab -e
Here’s what to add at the end of the crontab file:
1
0 1,13 * * * /home/ec2-user/certbot-auto renew
Simply copy-paste what’s above and then save/exit the text editor!
If everything went according to plan, you should be enjoying a fully functional HTTPS website using a free SSL certificate provided by Let’s Encrypt on your AWS EC2 Amazon Linux instance!
If it’s not working out as it should, comment below so that I can try to help!

